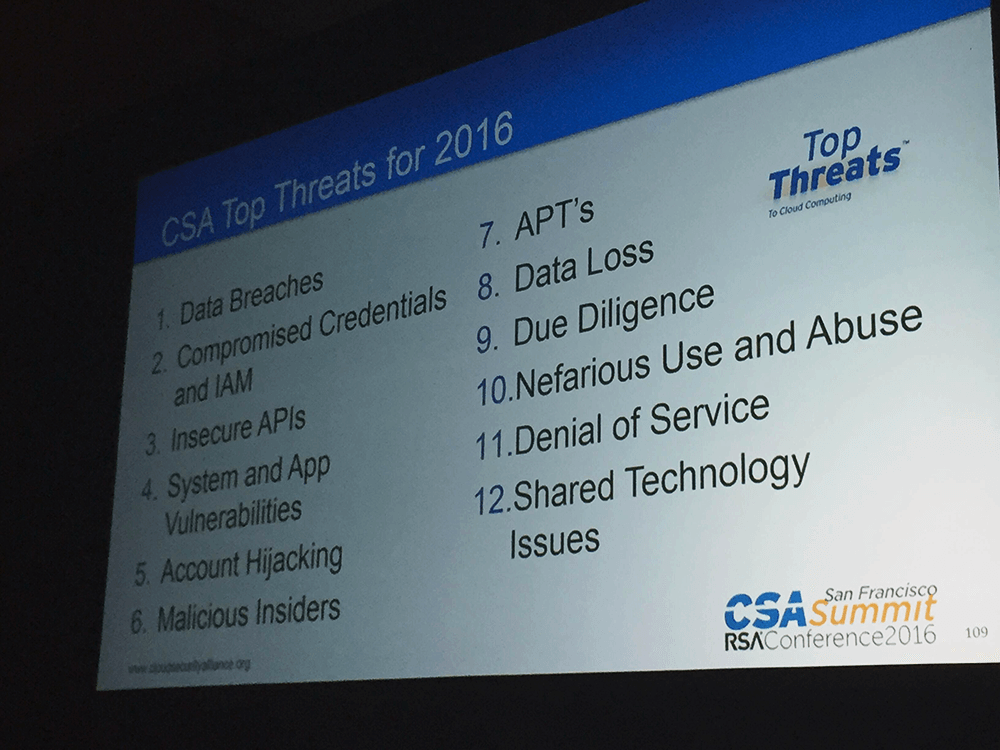
The Cloud Security Alliance (CSA) Top Threats Working Group published a report listing The Treacherous 12: Cloud Computing Top Threats in 2016:
- Data Breaches
- Weak Identity, Credential and Access Management
- Insecure APIs
- System and Application Vulnerabilities
- Account Hijacking
- Malicious Insiders
- Advanced Persistent Threats (APTs)
- Data Loss
- Insufficient Due Diligence
- Abuse and Nefarious Use of Cloud Services
- Denial of Service
- Shared Technology Issues

“Our last Top Threats report highlighted developers and IT departments rolling out their own self-service Shadow IT projects, and the bypassing of organizational security requirements. A lot has changed since that time and what we are seeing in 2016 is that the cloud may be effectively aligned with the Executive strategies to maximize shareholder value,” said Jon-Michael Brook, co-Chair of the Top Threats Working Group. “The ‘always on’ nature of cloud computing impacts factors that may skew external perceptions and, in turn, company valuations.”