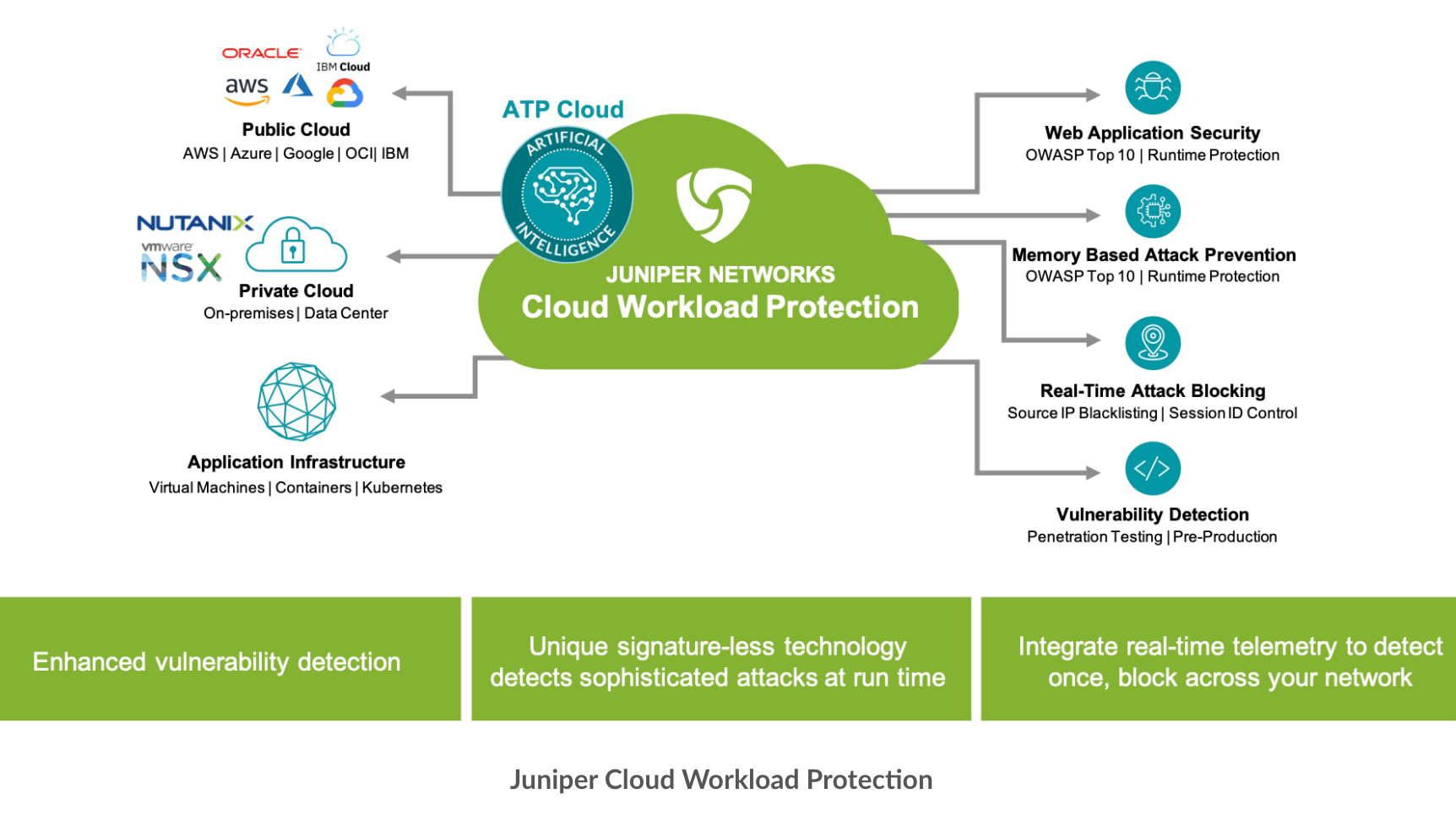
Juniper Networks introduced a Zero Trust Data Center architecture to automatically defend application workloads in any cloud or on-premises data center environment against application exploits as they happen, including the Open Web Application Security Project (OWASP) Top 10 and memory-based attacks.
Juniper Cloud Workload Protection is a lightweight software agent that controls application execution and monitors the application’s behavior and context, with vulnerability remediation is done automatically without admin intervention.
The company says its new product provides the following critical capabilities:
- Signatureless Run-Time Application Self-Protection (RASP) provides real-time protection against attacks. It protects the application from malicious actions, such as exploitation and data theft, without any manual intervention, catching sophisticated attacks that endpoint detection (EDR) and web application firewall (WAF) solutions cannot.
- Memory-Based Attack Prevention provides real-time protection against advanced memory-based attacks, including fileless, return-oriented programming (ROP) and buffer overflow attacks.
- Vulnerability Detection continuously assesses vulnerabilities in applications and containers to detect serious and critical exploit attempts as they happen. Juniper Cloud Workload Protection delivers information on the exploit attempt to DevSecOps teams to better understand where the vulnerability exists, so they can remediate.
- Comprehensive Telemetry provides rich application-level security event generation and reporting, including application connectivity, topology and detailed information about the attempted attack.
- Optimized Control Flow Integrity (OCFI) technology minimizes false alerts by validating the execution of applications and detecting attacks without using behavior or signatures.
- Zero Trust Microsegmentation shields application resources from lateral threat propagation and integrates with Juniper vSRX Virtualized Firewalls to restrict access based on risk, even as workloads and virtual environments change. Automated threat response with built-in, real-time telemetry helps security teams detect threats once and block them across the entire network.