by Tom Kelly, CEO, AccelOps
Why do armies set up look-outs all around their camps? Why do people read their horoscopes and shake magic eight-balls? Simple: they want to see what’s coming. In business, it’s incredibly helpful to be able to accurately forecast needs and set strategy. In the network security and performance arena of the business, it’s table stakes.
While there’s no crystal ball that can tell us everything, one thing is certain: organizations will need to fundamentally change the way they identify and manage threats. Below are my three predictions on this topic for the new year.
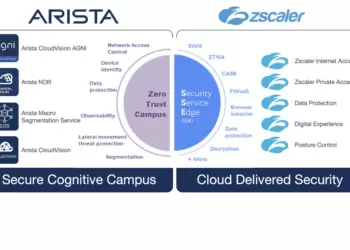
- It’s time to outsource security. With the unprecedented benefits and growth of the Internet of Things (IoT) and the vast number of touch points connecting to the network, new challenges and unknown risks associated with these tools will continue to multiply. Unknown risks include network and resource utilization, performance expectations and resource needs, interoperability with current systems and tools and, above all else, security risks and challenges to an organization’s livelyhood. As IT budgets shrink, and a shrinking pool of technical personnel, organizations will increasingly look outside their silos to managed security service providers (MSSP’s) for expert help.
- Organizations will map the customer journey. Consumers today have access to nearly infinite sources of information through the click of a mouse, resulting in a higher level of expectation for rapid answers from a variety of engagement channels. From websites to social media to mobile and multi-media, organizations are tasked with keeping up with customer demands from an ever-increasing set of “touch-points.” To that end, organizations will turn to tools that map and analyze a “360 view” of their customers’ journey and the respective “touch-points” throughout their organizations. As this integrated security and performance management requirement transitions from a tactical IT expenditure-driven initiative to a mission-critical, strategic business initiative, the era of CIOs and CISOs reporting to CFOs will shift to stronger oversight by boards of directors and CEOs.
- Businesses intelligence sources will converge. Proprietary customer and financial data and intellectual property are high-value targets for hackers. The challenge in protecting these targets will continue to grow as organizations become more reliant on business intelligence and analytics (Big Data) to dissect their various channels of customer engagement, workers, network and application productivity. As organizations store this valuable data in onsite and offsite locations (or a variety of both), Big Data is seen as a big target. These rich and proprietary sources of corporate analytics will spawn new and additional targets for hackers. Current silo-based approaches will need to converge with other business intelligence initiatives to provide more rapid identification and mitigation of risks.
Today’s dynamic, data-driven businesses have never been more reliant on the performance of their networks in managing risk and in the pursuit of their strategic initiatives. These same networks have never been more at risk for security breaches and the network performance impacts. With digital transformation in full swing, the pace of change is rapidly accelerating, and an organization’s ability to see into the network through solutions that provide a holistic, real-time view and correlation of the various elements in their network is becoming more critical than ever.
About the Author
 Tom Kelly is CEO of Accelops and a technology industry veteran having led companies through founding, growth, IPO and strategic acquisition. He has served as a CEO, COO or CFO at Cadence Design Systems, Frame Technology, Cirrus Logic, Epicor Software and Blaze Software. Tom led successful turnarounds at Bluestar Solutions, MonteVista Software and Moxie Software, having served as CEO in repositioning and rebranding the companies in advance of their new growth. He serves on the Boards of Directors of FEI, Fabrinet, and ReadyPulse. Tom is a graduate of Santa Clara University where he is member of the University’s Board of Regents.
Tom Kelly is CEO of Accelops and a technology industry veteran having led companies through founding, growth, IPO and strategic acquisition. He has served as a CEO, COO or CFO at Cadence Design Systems, Frame Technology, Cirrus Logic, Epicor Software and Blaze Software. Tom led successful turnarounds at Bluestar Solutions, MonteVista Software and Moxie Software, having served as CEO in repositioning and rebranding the companies in advance of their new growth. He serves on the Boards of Directors of FEI, Fabrinet, and ReadyPulse. Tom is a graduate of Santa Clara University where he is member of the University’s Board of Regents.
Got an idea for a Blueprint column? We welcome your ideas on next gen network architecture.
See our guidelines.