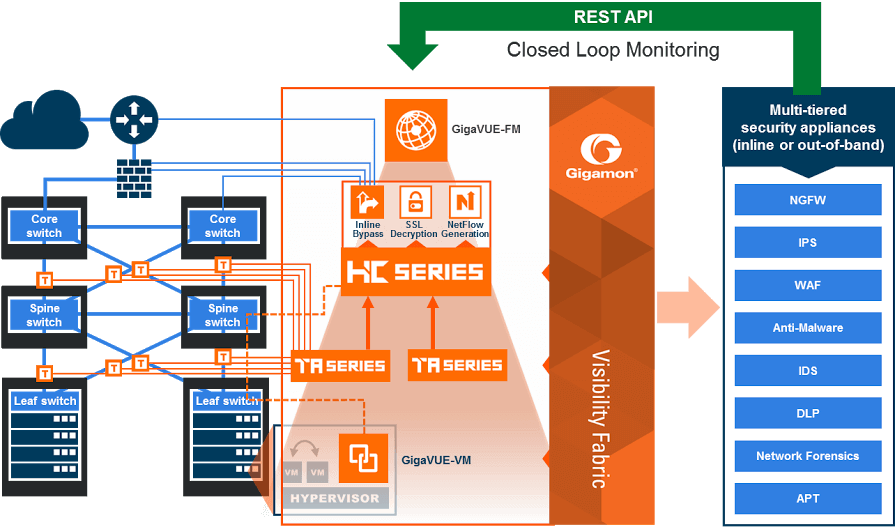
Gigamon outlined its framework for leveraging software-defined intelligent traffic visibility to automatically detect threats and then programmatically adapt security policies.
Gigamon outlined its framework for leveraging software-defined intelligent traffic visibility to automatically detect threats and then programmatically adapt security policies.
“Software Defined Visibility is a first of its kind breakthrough. It enables security tools, such as IPSs, WAFs, Secure Web Gateways, Sandboxes and other in-line or out-of-band security appliances to program the Gigamon Visibility Fabric to automatically update traffic Flow Maps and GigaSMART operations based on real-time conditions,” said Shehzad Merchant, chief technology officer at Gigamon. “By enabling the programmability of our Visibility Fabric, customers gain the ability to dynamically adjust and enhance their visibility posture thereby improving security, while reducing costs and network complexities.”
Software Defined Visibility is a framework that allows customers, security and network equipment vendors, as well as managed service providers, to control and program Gigamon’s Visibility Fabric via REST-based Application Program Interfaces (APIs). By writing programs that utilize Gigamon’s APIs, critical functions previously requiring manual intervention can be automated to improve responsiveness, enhance analysis and increase protection of key resources and information assets. Potential use case examples include:
- Improve Security Efficiencies – Security administrators can develop applications to improve network detection, reaction and response by automating NetFlow generation and SSL decryption so that current security appliances are not overtaxed when performing deep packet inspection. For example, administrators can use the APIs that program the Visibility Fabric to dynamically change the traffic forwarding policies in response to threats or anomalous network traffic changes.
- Automate Policy Management – As new virtual machines are spun up, administrators can write policy management programs that utilize Gigamon’s APIs to automatically follow new changes within virtual and physical networks.
- Simplify Provisioning and Ticketing – For many organizations, IT Operations Management (ITOM) groups are burdened to manually perform common tasks, such as provisioning and ticketing of network port configurations, monitoring of new IP subnets and VLANs, and upgrading software images. With Software Defined Visibility, ITOM groups can develop programs to automate these processes.
The new capabilities are enabled in GigaVUE-FM 3.0 Fabric Manager, which delivers a single pane-of-glass view of physical and virtual nodes across the Visibility Fabric. A single instance of GigaVUE-FM can manage hundreds of visibility nodes across multiple locations, containing more than a quarter of a million physical ports in addition to managing virtual infrastructures.
Flow Mapping technology helps reduce traffic and improve analyzer performance. Flow Mapping is a patented technology at the heart of Gigamon’s GigaVUE Visibility Fabric nodes that takes line-rate traffic at 1Gb, 10Gb, 40Gb or 100Gb from a network TAP or a SPAN/mirror port (physical or virtual) and then optimizes flows based on individual traffic profiles of the tools and applications that secure, monitor, and analyze the network infrastructure.
http://www.gigamon.com