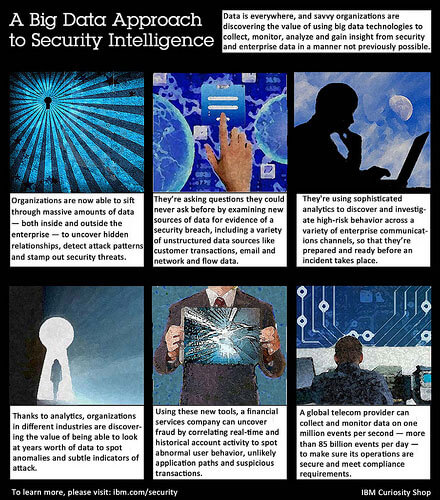
IBM introduced a solution that combines security intelligence with big data analytics capabilities for both external cyber security threats and internal risk detection and prevention. The goal is to allow security analysts to extend their analysis well beyond typical security data and to hunt for malicious cyber activity.
 The IBM Security Intelligence with Big Data solution combines real-time correlation for continuous insight, custom analytics across massive structured data (such as security device alerts, operating system logs, DNS transactions and network flows) and unstructured data (such as emails, social media content, full packet information and business transactions), and forensic capabilities for evidence gathering. IBM said this combination provides deeper insight into advanced persistent threats, fraud and insider threats.
The IBM Security Intelligence with Big Data solution combines real-time correlation for continuous insight, custom analytics across massive structured data (such as security device alerts, operating system logs, DNS transactions and network flows) and unstructured data (such as emails, social media content, full packet information and business transactions), and forensic capabilities for evidence gathering. IBM said this combination provides deeper insight into advanced persistent threats, fraud and insider threats.
Key elements of the solution include:
- Real-time correlation and anomaly detection of diverse security and network data
- High-speed querying of security intelligence data
- Flexible big data analytics across structured and unstructured data – including security, email, social media, business process, transactional, device, and other data
- Graphical front-end tool for visualizing and exploring big data
- Forensics for deep visibility into network activity
IBM cited the Depository Trust & Clearing Corporation (DTCC) as a potential beneficiary of this big data cyber analysis approach.
“As the sophistication and technological means of cyber-criminals increase, the financial industry and government need to move to a risk-based framework that incorporates the dynamic nature of the threat landscape,” said Mark Clancy, CISO, Managing Director, Technology Risk Management, DTCC. “We need to move from a world where we ‘farm’ security data and alerts with various prevention and detection tools to a situation where we actively ‘hunt’ for cyber-attackers in our networks. IBM’s Security Intelligence with Big Data solution gives us a practical way to gain visibility across our environment. We’re gaining real-time security awareness and meaningful insight into historical activity across years of diverse data.”