Intel is introducing a new security capability in its silicon microarchitecture to help protect against common malware attack methods that have been a challenge to mitigate with software alone.
 Intel’s new Control-Flow Enforcement Technology (Intel CET), which will be first available on Intel’s upcoming mobile processor code-named “Tiger Lake,” is designed to protect against the misuse of legitimate code through control-flow hijacking attacks – widely used techniques in large classes of malware.
Intel’s new Control-Flow Enforcement Technology (Intel CET), which will be first available on Intel’s upcoming mobile processor code-named “Tiger Lake,” is designed to protect against the misuse of legitimate code through control-flow hijacking attacks – widely used techniques in large classes of malware.
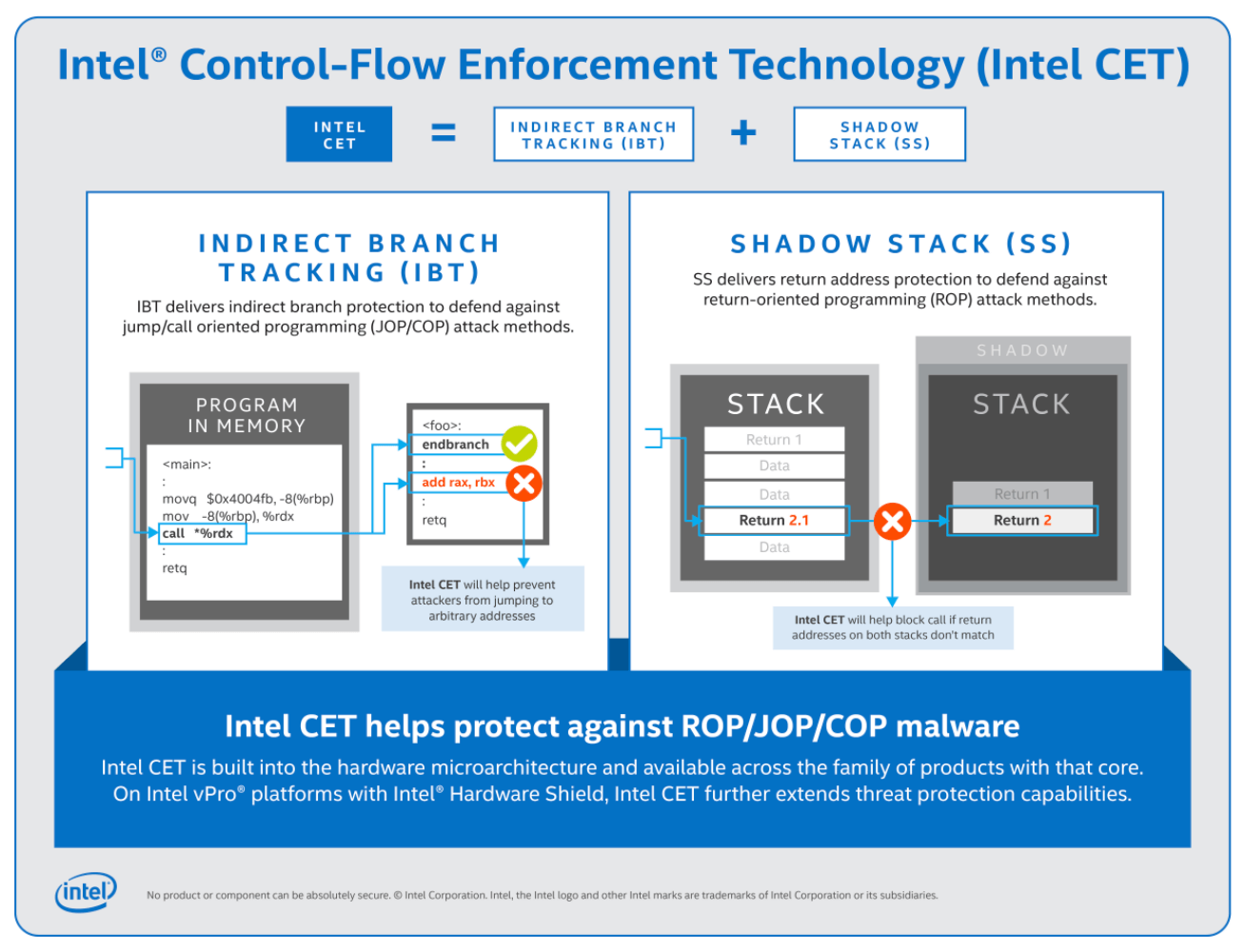
Intel CET offers software developers two key capabilities to help defend against control-flow hijacking malware: indirect branch tracking and shadow stack. Indirect branch tracking delivers indirect branch protection to defend against jump/call-oriented programming (JOP/COP) attack methods. Shadow stack delivers return address protection to help defend against return-oriented programming (ROP) attack methods. These types of attack methods are part of a class of malware referred to as memory safety issues and include tactics such as the corruption of stack buffer overflow and use-after-free.
Microsoft’s support Intel CET in Windows 10 is called Hardware-enforced Stack Protection, and a preview of it is available today in Windows 10 Insider Previews. This new Hardware-enforced Stack Protection feature only works on chipsets with Intel CET instructions. It relies on a new CPU architecture that is compliant with Intel CET specifications. For applications running on an OS that supports Intel CET, users can expect detailed guidance from our partners on how applications “opt-in” for protection.